Linux Is No Longer Immune: Why Ransomware Gangs Are Going All-In on Linux Targets
For years, Linux was seen as the quiet giant of enterprise infrastructure—reliable, stable, and far less targeted than Windows. That time is over.
With ransomware operators now eyeing Linux as fertile ground for disruption and financial gain, CISOs can no longer afford to treat Linux environments as inherently secure or low risk. As cloud adoption surges and Linux cements its place across critical workloads, attackers are adapting—and they’re hitting harder than ever.
It’s time for a wake-up call.
Linux Has a Target on Its Back
Linux now powers over 80% of public cloud workloads and 96% of the top million web servers. It’s the backbone of critical applications, APIs, DevOps pipelines, and virtual infrastructure. That’s precisely what makes it so attractive to ransomware gangs.
The perception that Linux is “secure by default” has become a dangerous blind spot. Threat actors are no longer repurposing Windows malware—they’re building Linux-native ransomware, specifically designed to bypass traditional detection and response tools and thrive in resource-constrained environments.
Just consider recent headlines:
- Pay2Key updated ransomware build designed to target Linux based systems in the builder options.
- Helldown ransomware expands its scope to VMware and Linux.
- BERT ransomware weaponizes Linux ELF files.
The threat is clear—and it’s growing.
Attackers Are Moving Faster, and Smarter
Today’s ransomware campaigns don’t follow the playbooks of the past. They are faster, more evasive, and more sophisticated; they’re designed to exploit exactly where Linux is weakest. Here’s how attackers are gaining the upper hand:
- Fileless Execution and Living-off-the-Land (LotL) Tactics — Rather than dropping traditional payloads, attackers increasingly use LotL techniques, leveraging built-in Linux tools like Bash scripts, cron jobs, and systemd services to execute malicious code entirely in memory. These fileless attacks don’t leave artifacts on disk, making them invisible to traditional EDR, antivirus, and behavior-based defenses.
- Double Extortion Is the New Normal — Linux ransomware isn’t just encrypting systems—it’s also exfiltrating sensitive data. Attackers then demand ransom not just to restore access, but to prevent public exposure of critical IP, financial data, or customer records. This combination raises the stakes and the price tag.
- Cloud and DevOps Environments Are Prime Targets — Because Linux powers most cloud-native environments, attackers are tailoring their ransomware to exploit cloud misconfigurations, weak permissions, and CI/CD pipelines. Containers and Kubernetes clusters are particularly vulnerable—offering rapid lateral movement once initial access is gained.
The pace and scale of modern Linux deployments create opportunities for attackers to strike before teams even realize there’s a gap.
Why Traditional Defenses Fall Short
Most Linux environments today rely on reactive, detection-based tools—legacy antivirus, file scanning, or EDR platforms ported over from Windows ecosystems. But those tools are built for a different era—and a different OS.
Here’s where they fail:
- Blind to Memory-Based Attacks: Most tools rely on disk scanning or behavioral signatures, which do nothing against in-memory threats.
- Fragmentation Kills Visibility: With dozens of Linux distributions and configurations, coverage is inconsistent at best—and nonexistent at worst.
- Resource Constraints Limit Protection: Lightweight Linux systems can’t afford the performance overhead that traditional security tools require.
CISOs need a fundamentally different approach to Linux security—one that doesn’t depend on detection after the fact but instead prevents attacks from executing in the first place.
The Shift to Preemptive Cyber Defense
To protect Linux systems from modern ransomware, organizations must embrace a prevention-first strategy. That means abandoning the outdated assumption that threats can be detected before they cause harm.
Instead, the new standard is deterministic prevention—neutralizing ransomware before it runs, regardless of how it was delivered or what it’s designed to do.
Solutions like Morphisec’s Anti-Ransomware Assurance Suite embody this shift by leveraging deception-based decoys to bait and stop ransomware before encryption or exfiltration begins; memory shielding that blocks in-memory execution paths, and zero-noise protection that eliminates false positives.
CISOs gain peace of mind that their Linux systems are protected—even from fileless, zero-day, and polymorphic threats.
The result? Faster recovery, fewer breaches, and a dramatically reduced attack surface.
How Morphisec Stops Linux Ransomware—Before It Starts
Morphisec’s Anti-Ransomware Assurance Suite is purpose-built to defend Linux systems in today’s threat environment—where ransomware operates in-memory, leverages trusted Linux utilities, and bypasses traditional defenses altogether.
Here’s what makes it stand out:
- Stops Ransomware Pre-Execution:
Morphisec blocks ransomware before it encrypts files or exfiltrates data. Its deception-based defense deploys high-value decoys that lure ransomware to expose itself in the earliest stage of execution, triggering automatic prevention—without relying on behavior analytics or prior threat knowledge. - Immune to Fileless and Zero-Day Attacks:
Unlike signature-based tools, Morphisec doesn’t need to recognize malware to block it. Its memory shielding technology prevents payloads—no matter how novel or polymorphic—from running in system memory. Even if a zero-day exploit slips through, it can’t detonate. - Lightweight and Scalable:
Built with Linux in mind, the solution delivers near-zero performance impact and seamless integration across diverse infrastructures—from VMs and containers to CI/CD pipelines and connected devices. No tuning, no scanning, no operational disruption. - Reduces Response Time and Complexity:
With deterministic protection, there’s no waiting for detection or chasing down alerts. Threats are neutralized automatically, reducing the burden on security teams and enabling fast, confident recovery. - Ensures Adaptive Recovery:
This groundbreaking solution is designed to provide comprehensive ransomware resilience. By combining Data Recovery and Forensic Recovery, Adaptive Recovery ensures businesses can recover encrypted files in real-time while preserving critical forensic data for rapid investigation and compliance.
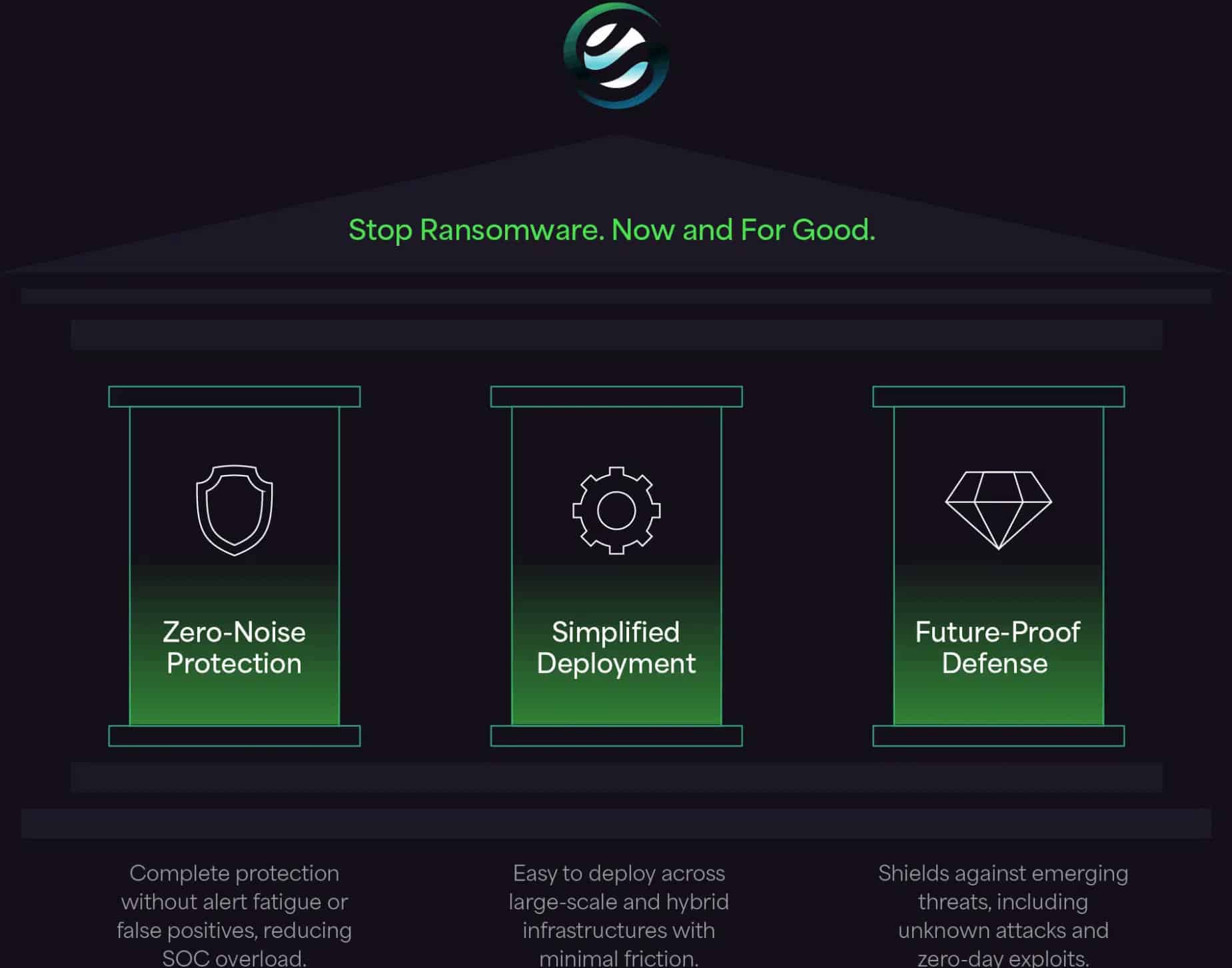
In a landscape where ransomware moves faster than ever, Morphisec provides Linux environments with something rare: control, clarity, and confidence.
Rethink What “Protected” Means
The Linux ecosystem is under siege—not just from opportunistic criminals, but from state-sponsored actors and supply chain attackers who understand the platform’s weaknesses and exploit its strengths.
As a CISO, you’re charged with protecting the systems that run your business. It’s time to ask yourself:
Are your Linux defenses built for the threat landscape we face today—or the one we left behind?
Download the Securing Linux Systems Against Emerging and Evasive Ransomware white paper to access an in-depth guide on Linux-specific ransomware threats and how to stop them with preemptive cyber defense.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.