AI-Enabled Ransomware Demands AI-Enabled Defense — Not Just Better Recovery
Ransomware recovery is getting more sophisticated.
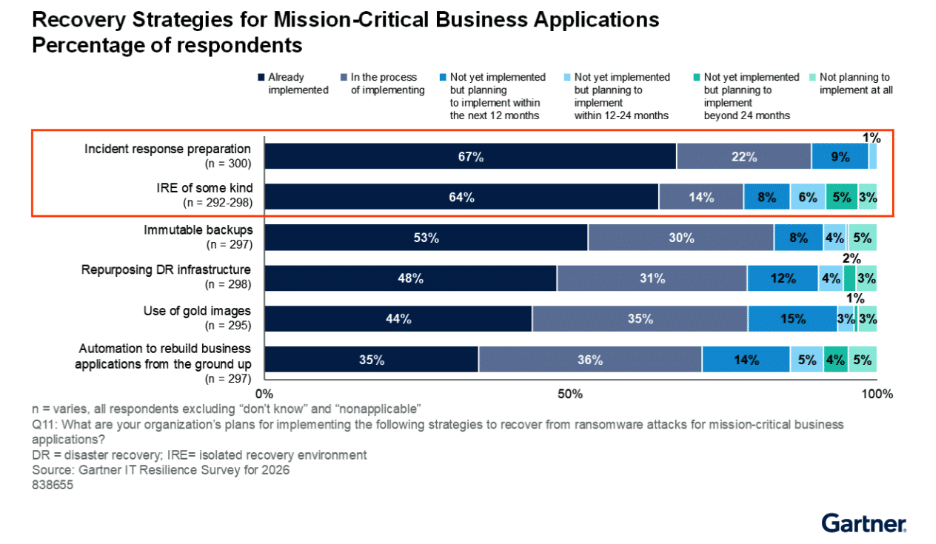
According to Gartner’s IT Resilience Survey for 2026: Ransomware Recovery and Readiness1, organizations have made meaningful progress in strengthening foundational recovery capabilities.
Sixty-seven percent have implemented incident response preparation. Nearly 70% report deploying backup software with automation capabilities. Many are investing in isolated recovery environments (IREs), immutable backups, and infrastructure-as-code (IaC) modernization.
On paper, resilience appears to be improving.
And yet, Gartner’s research also reveals a more sobering reality: despite these investments, many organizations still struggle to leverage recovery capabilities effectively. A lack of integrated strategy, complex coordination between IT and business leaders, and operational gaps continue to lead to prolonged downtime, data loss, and elevated costs.
The industry is getting better at cleaning up ransomware. But cleaning up is not the same as preventing impact. In 2026, as ransomware becomes increasingly AI-enabled, resilience must evolve beyond “better recovery.”
It must shift toward AI-enabled prevention.
The Recovery Arms Race
Gartner’s findings show a clear trend: organizations are doubling down on advanced recovery strategies. And automation is becoming central to ransomware recovery. Organizations are codifying servers, networks, configurations, and security policies. They are preparing to rebuild faster, cleaner, and more predictably.
But here’s the tension. Even with advanced automation and modernized infrastructure, ransomware recovery remains expensive for resilience.
You still experience:
- Application downtime
- Business disruption
- Crisis coordination
- RTO negotiations with executives
- Regulatory scrutiny
- Brand impact
Faster recovery is still reactive security. And in an AI-driven threat landscape, reactive security is increasingly under pressure.
AI Is Accelerating the Ransomware Lifecycle
Ransomware attacks today are not static scripts executed manually by human operators. They are becoming AI-assisted and increasingly autonomous.
AI-enabled ransomware campaigns can:
- Automate reconnaissance
- Accelerate lateral movement
- Adapt payloads dynamically
- Exploit zero-day vulnerabilities
- Target and corrupt backups
- Obfuscate behaviors to evade traditional detection tools
Gartner rightly notes that traditional disaster recovery strategies are often insufficient for modern ransomware threats, particularly because attackers now deliberately target backup environments.
What becomes more concerning in 2026 is the speed. AI compresses the attack timeline.
The dwell time between initial compromise and encryption shrinks. The time available for detection and response narrows. Automation is no longer exclusive to defenders; it is embedded in the attacker’s toolkit.
The result?
Organizations may invest heavily in recovery sophistication, only to find that AI-accelerated attacks hit faster, spread further, and execute before traditional detection-based controls can respond. In this environment, resilience must move upstream.
Automation Alone Doesn’t Eliminate Compromise
Gartner highlights broad adoption of automation in backup and recovery tooling. This is positive progress. But automation accelerates restoration; it does not eliminate compromise.
You can:
- Restore immutable backups
- Spin up clean infrastructure from code
- Rebuild applications automatically
- Re-platform environments
But you cannot erase the fact that encryption occurred.
You cannot eliminate the operational interruption that triggered crisis management.
You cannot undo the executive-level escalation, the customer communication, the regulatory exposure, or the reputational risk.
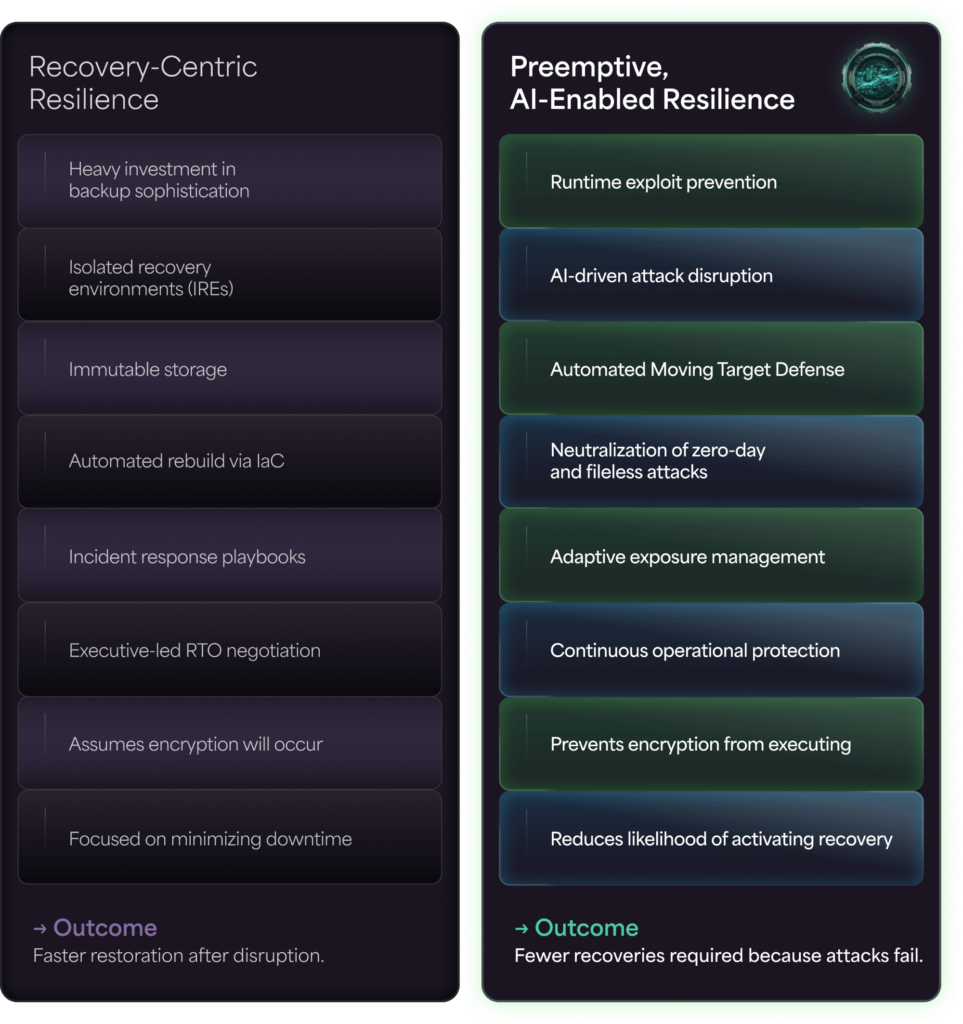
Recovery-first resilience assumes that compromise is inevitable. That assumption made sense in a purely detection-driven era. It becomes increasingly costly in an AI-enabled one.
The Mindset Shift: From Recovery-Centric to Preemptive Resilience
Gartner emphasizes that business involvement in recovery time objective (RTO) establishment correlates with more sophisticated recovery strategies. When executives participate in defining acceptable downtime, recovery becomes a business conversation…not just a technical one.
But there’s a deeper question leaders should be asking: Why are we designing for recovery as the primary outcome? In 2026, the most resilient organizations will not simply recover faster. They will experience fewer recoveries.
This requires a shift from recovery-centric resilience to preemptive resilience.
Instead of assuming the attack will execute and preparing to rebuild, organizations must focus on disrupting the attack chain before ransomware can detonate.
That means:
- Preventing exploit execution at runtime
- Neutralizing memory-based and fileless attacks
- Disrupting zero-day exploitation
- Invalidating automated attack chains
- Rendering attacker reconnaissance unreliable
This is where AI-enabled defense becomes critical.
AI-Enabled Ransomware Requires AI-Enabled Defense
If attackers are using automation and AI to accelerate exploitation, defenders must respond with automation and AI that neutralize threats in real time, not simply analyze them after detection.
AI-enabled defense is not just about smarter analytics. It is about automated disruption.
It means:
- Runtime exploit prevention
- Automated Moving Target Defense (AMTD) techniques that randomize and obscure memory structures
- Deception-driven controls that invalidate attacker assumptions
- Autonomous neutralization of zero-day techniques
- Prevention of encryption execution before payload detonation
This approach shifts resilience from “restore after impact” to “continue operating without interruption.”
In practical terms, that changes everything:
- RTO conversations become less urgent
- Crisis governance becomes less frequent
- Downtime economics improve dramatically
- Regulatory exposure decreases
- Cyber insurance posture strengthens
Prevention reduces the blast radius before it forms.
Recovery Is the Safety Net, Not the Strategy
To be clear: recovery still matters. Immutable backups. Isolated recovery environments. Infrastructure automation. These are essential safety nets. But safety nets are not primary strategies.
As ransomware becomes AI-enabled and increasingly autonomous, organizations cannot afford to design resilience programs around the assumption of inevitable compromise.
The economics no longer support it.
The operational complexity no longer supports it.
The executive risk tolerance no longer supports it.
True resilience in 2026 will be defined not by how quickly you rebuild, but by how effectively you prevent ransomware from executing in the first place.
Recovery will always have a role. But in an AI-accelerated threat landscape, the leaders who outperform will be those who shift from reactive restoration to preemptive disruption…moving from cleaning up ransomware to stopping it before it starts.
In the end, the strongest resilience metric may not be your RTO. It may be how rarely you have to use it.
See how Morphisec’s Anti-Ransomware Assurance Suite can help your business stop attacks before they start — book a demo today.
1 Gartner IT Resilience Survey for 2026: Ransomware Recovery and Readiness, Ajeeta Malhotra, Ron Blair, 15 September 2025
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.