Mission-Critical Preemptive Cybersecurity in Oil and Gas: Key Insights for CISOs and Cybersecurity Professionals
In Episode 248 of the OGGN HSE Podcast, Morphisec’s own Brad LaPorte sat down to discuss the evolving cybersecurity challenges in the oil and gas sector.
Below, we’ve delved deeper into the critical takeaways for CISOs, cybersecurity leaders, and those tasked with securing critical infrastructure in the energy sector.
Why the Oil and Gas Sector is a Prime Target
The energy industry has become a top target for cybercriminals due to its critical role in powering economies and its reliance on interconnected systems. According to Brad, it’s no longer just about protecting financial institutions; ransomware gangs now view industries like oil and gas as lucrative and vulnerable targets. The combination of legacy systems, regulatory challenges, and broad attack surfaces makes oil and gas an attractive sector for cyberattacks.
These stats highlight the rising risk:
- Ransomware on the Rise: Attacks in the oil and gas sector have increased to almost 1,000% in the last year, according to reports.
- Increased Ransom Payments: Median ransom payouts grew by 100% in 2025, with average demands now exceeding $1.13m+ and median payment exceeding $400,000+. 2 in 3 of payments occurred because backups failed. 1 in 3 payments were driven by the desire to prevent the release of exfiltrated information.
- AI-Driven Cybercrime: Ransomware gangs are leveraging AI for faster reconnaissance, automated vulnerability discovery, and highly targeted attacks, making them faster and more precise.
Case Study: The Colonial Pipeline Incident
The Colonial Pipeline attack remains a defining moment in cybersecurity for critical infrastructure with Brad highlighting how the Russian-affiliated DarkSide group exploited a single VPN vulnerability to deploy ransomware, shutting down 5,500 miles of pipeline that supplied nearly half of the East Coast’s fuel.
What Went Wrong:
- Lack of multi-factor authentication (MFA) for VPN access.
- Overreliance on outdated VPN-based access controls.
- Insufficient preemptive safeguards to stop ransomware at the pre-execution stage.
Impact:
- Colonial Pipeline paid 75 Bitcoin (approximately $4-5 million) in ransom.
- Recovery efforts took over a year and cost billions in operational and reputational damage.
These incidents are not isolated. Many organizations in the energy sector face similar vulnerabilities due to legacy systems (with many organizations still being forced to utilize Windows XP), underfunded cybersecurity budgets, and a lack of preemptive defense strategies.
Why Traditional Security Tools Fall Short
Traditional cybersecurity tools often focus on Detect and Respond, which means they only act after an attacker has breached the system. Brad explained that by the time these tools trigger an alert, significant damage, such as data exfiltration, encryption, or operational shutdowns, may already be underway.
Challenges with Detection-Based Solutions:
- Attackers bypass defenses by exploiting zero-day vulnerabilities or using legitimate IT tools in malicious ways.
- Solutions like EDR and XDR often struggle to detect advanced threats, such as fileless malware and in-memory attacks.
- Ransomware gangs increasingly target backups, encrypting or exfiltrating them to force ransom payments.
How Morphisec Stands Apart: Preemptive Cybersecurity with AMTD
Brad made it clear: the industry needs to shift from a reactive, detection-based approach to cybersecurity, to a proactive and preemptive stance.
Morphisec’s preemptive approach to Anti-Ransomware leverages its patented Automated Moving Target Defense (AMTD) technology, which is a game-changer for securing critical infrastructure. Unlike traditional tools, Morphisec stops ransomware and other advanced threats before execution by dynamically morphing runtime memory, creating an unpredictable attack surface that attackers cannot exploit. This protection follows the entire full extent of a full attack with mitigation steps pre, during, and post execution of an attack. Giving you full peace of mind and assurance that you are protected from ransomware and other sophisticated attacks on your critical infrastructure.
Here’s how it works:
- Morph and Conceal: Runtime memory and underlying attack surface is continuously morphed, making it impossible for attackers to locate their target.
- Protect and Deceive: Attackers are directed to decoys and traps, neutralizing their efforts.
- Prevent and Expose: Malicious processes are stopped before execution, and forensic data is captured for post-incident analysis.
And the results?
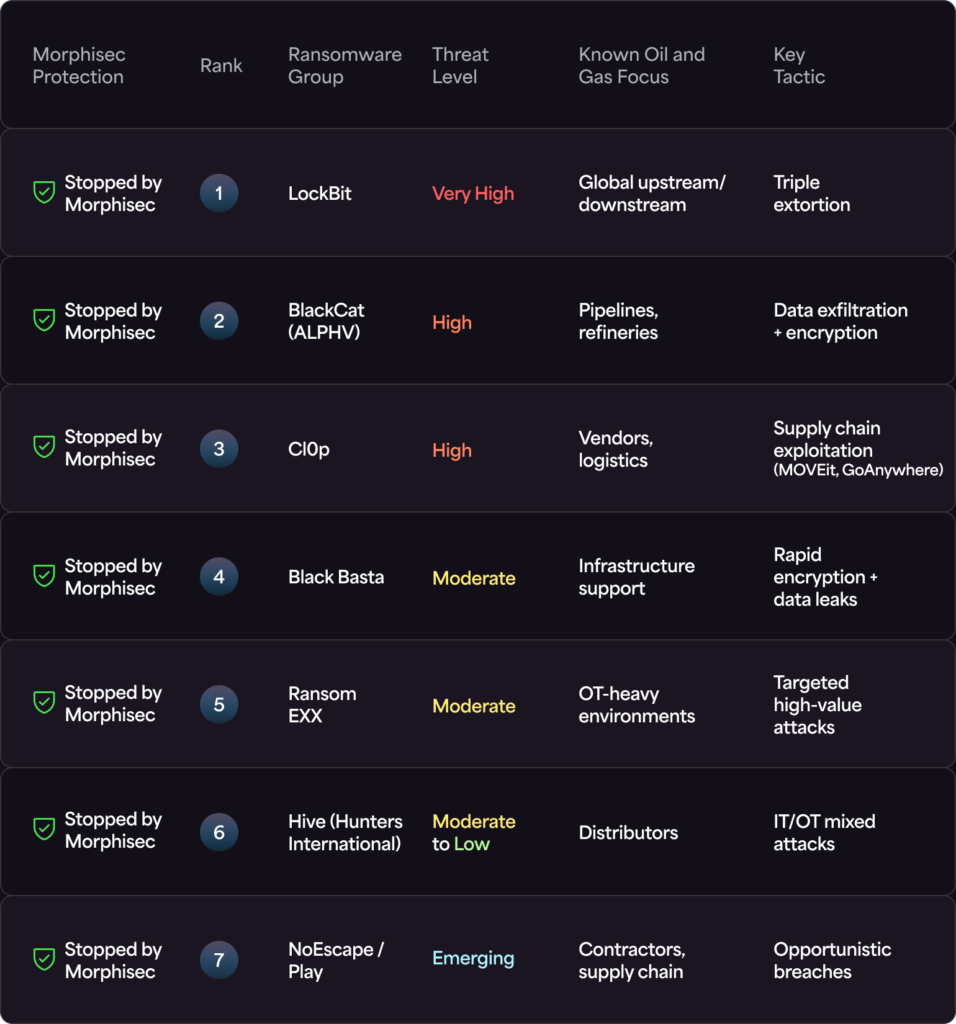
- Morphisec stops advanced threats like LockBit, BlackCat (ALPHV), Cl0p, Black Basta, RansomEXX, Hive (Hunters International), NoEscape, and Play that evade traditional tools.
- It prevents lateral movement, privilege escalation, and data exfiltration.
- The platform requires no manual tuning, making it a lightweight, automated solution.
Morphisec: The Digital PPE for Critical Infrastructure
The episode drew a compelling analogy between Morphisec and personal protective equipment (PPE), where Brad suggested that “Just as workers rely on helmets and gloves to prevent physical harm, organizations need preemptive cybersecurity solutions to prevent digital harm.” Morphisec acts as a safety net, working alongside existing tools like Microsoft Defender, CrowdStrike, and SentinelOne to stop threats before they can disrupt operations.
A Call to Action for CISOs
Ransomware continues to rapidly increase in volume, impact and sophistication; it’s evolving faster than most defenses can keep up with. As Brad emphasizes, this is no longer just an IT issue, it’s a business-critical concern that impacts safety, profitability, and operational resilience.
Morphisec’s prevention-first approach offers the energy sector a proven solution for mitigating ransomware risks, ensuring uninterrupted operations, and protecting critical assets.
Tune into the full podcast for more insights.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.