AI Broke Your Security Model — Gartner® Says It’s Time for Preemptive Defense
AI didn’t just accelerate cyberattacks. It broke the assumptions modern security was built on.
For years, organizations have relied on detection and response as the backbone of their security strategy. But today’s attackers aren’t playing by those rules. They’re using generative and agentic AI to move faster, adapt in real time, and bypass controls that were never designed to stop threats before execution.
And now, Gartner is making it official.
In its latest research, Emerging Tech: Top Solution Capabilities in Preemptive Cybersecurity, Gartner outlines a clear shift: organizations must move beyond reactive detection and adopt preemptive cybersecurity strategies that deny, deceive, and disrupt attacks before they succeed.
Download the complimentary Gartner report to explore the full findings:
The Breaking Point: AI Has Outpaced Detection
Attackers are no longer constrained by time, tooling, or scale.
AI-generated malware can morph in real time. Autonomous attack chains eliminate manual effort. Fileless and memory-based techniques bypass traditional controls entirely. And perhaps most critically, attacks now unfold faster than humans (or detection tools) can respond.
As per our knowledge, Gartner highlights a harsh reality1:
- AI enables attackers to bypass traditional controls with unprecedented sophistication
- The speed of exploitation now exceeds human response capabilities
This is the AI security gap in action.
It’s not a visibility problem. It’s not a tooling problem. It’s a time problem. By the time an alert is triggered, the damage is already in motion. If your strategy starts with detection, you’re already late.
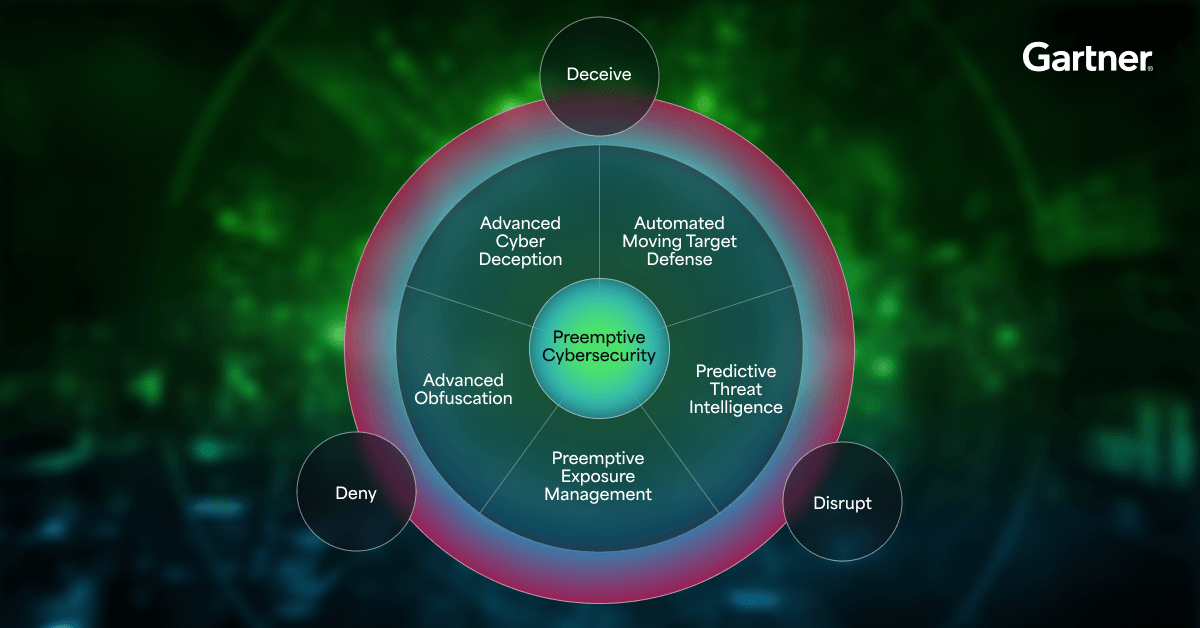
Gartner Answer: Preemptive Cybersecurity
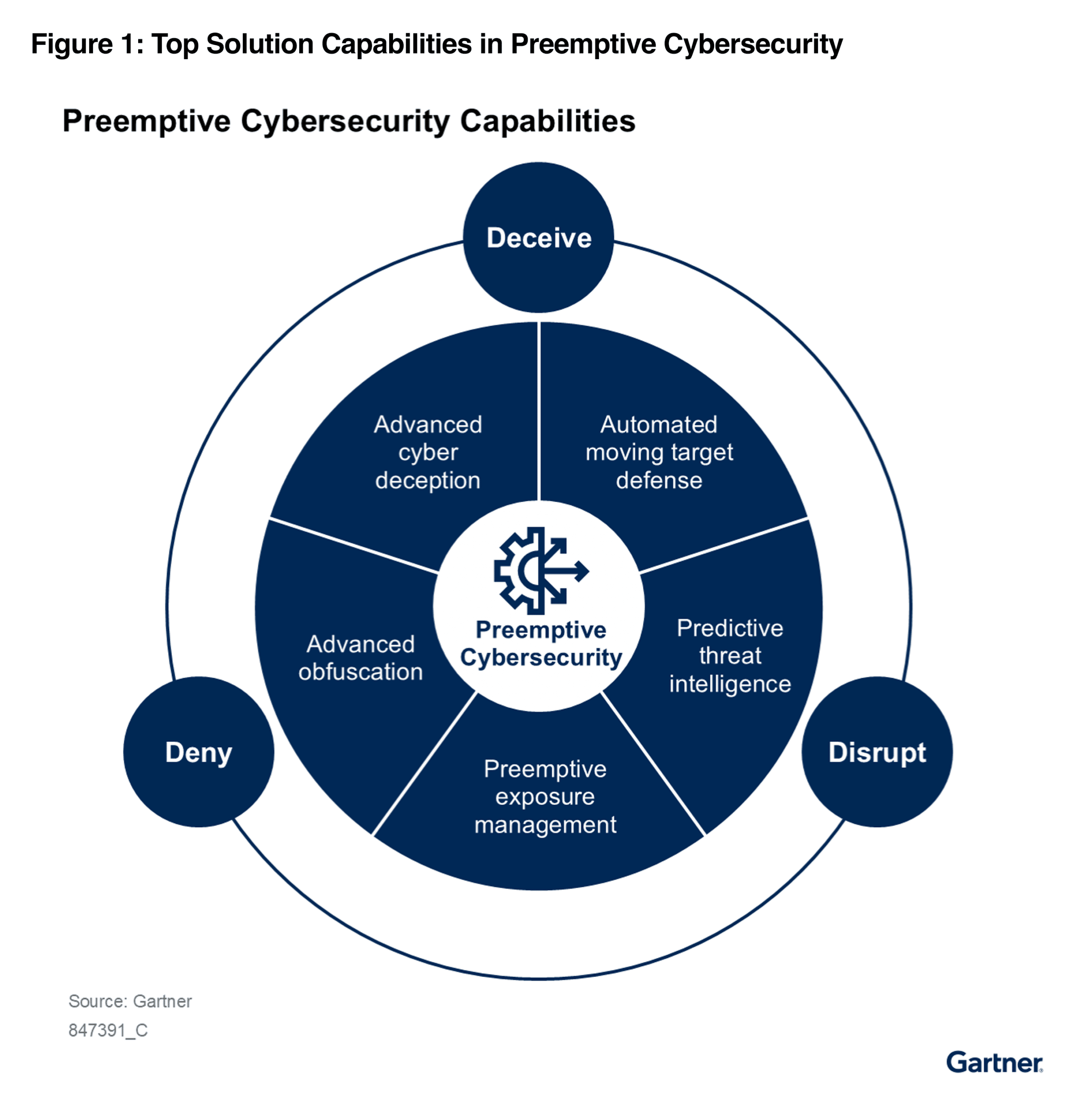
To keep up, security must change; not incrementally, but fundamentally. Gartner defines preemptive cybersecurity as an approach that takes automated, real-time, anticipatory action to deny, disrupt or deceive adversaries.
At its core, this model is built on three outcomes:
- Deny attackers access to viable targets
- Deceive them with false signals and environments
- Disrupt their ability to execute attacks
This represents a complete shift in how security operates:
- From alerts → automated action
- From investigation → interruption
- From response → prevention
This isn’t just a new layer in the stack. It’s a new operating model for cybersecurity.
What Defines Preemptive Security?
Gartner outlines the core capabilities organizations must adopt to make this shift:
- Automated Moving Target Defense (AMTD)
Shifts Threat Detection to Active Prevention by Disrupting AI-Driven Attacks Early. - Advanced Cyber Deception & Obfuscation
Shifts the Balance of Power by Weaponizing the Attack Surface With AI-Driven Decoys. - Predictive Threat Intelligence (PTI)
Anticipates and Helps Neutralize AI-Driven Attacks Before They Occur. - Preemptive Exposure Management
Evolves Beyond Visibility to Deliver Autonomous Interdiction.
The takeaway: Preemptive security doesn’t wait to see what happens. It changes the conditions so attacks can’t succeed in the first place.
Detection vs. Preemptive Security: What’s the Difference?
Here’s where the shift becomes crystal clear:
| Detection-Based Security | Preemptive Cybersecurity |
| Identifies threats after activity begins | Stops threats before execution |
| Relies on signatures, behavior, and alerts | Uses deception, obfuscation, and dynamic environments |
| Requires human investigation and response | Automates disruption in real time |
| Reactive and event-driven | Proactive and continuous |
| Measures time to detect/respond (MTTD/MTTR) | Measures time to prevent/neutralize (MTTN) |
| Assumes breach is inevitable | Works to make breach impossible |
This is the shift Gartner is calling for. And it’s happening faster than most organizations realize.
Gartner predicts1:
- By 2030, preemptive cybersecurity solutions will be incorporated into 50% of IT security
spending - By 2030, preemptive cybersecurity technologies will be included in 75% of security solutions that are currently focused solely on detection and response.
This is a platform-level transformation, not a niche trend. Organizations that continue investing solely in detection and response will find themselves defending against modern threats with outdated models.
And it isn’t just a concept; it’s already delivering real-world results. In a Gartner-cited use case, an enterprise organization replaced its legacy security stack with an AMTD-based memory protection solution.
Instead of detecting attacks, the system continuously reshaped runtime memory, making it impossible for attackers to predict or exploit.
The result?
- Malicious injections failed instantly
- Credential harvesting attempts were neutralized
- False positives dropped by 95%
When attackers can’t understand the environment, they can’t succeed.
Where Morphisec Leads the Shift to Preemptive Defense
While many organizations are just beginning to explore preemptive security, Morphisec has been building toward this model from the start.
- A Pioneer in Automated Moving Target Defense
Morphisec’s core deception technology continuously reshapes runtime environments, preventing fileless attacks, memory exploits, zero-day threats and more, before they can execute. - Adaptive AI Defense for the AI Threat Era
As attackers weaponize AI, Morphisec is using it to preempt them. Adaptive AI Defense protects against autonomous attack chains, AI-generated malware and rogue AI agents by stopping threats before they gain a foothold. - Adaptive Exposure Management
Morphisec extends beyond protection into proactive risk reduction. Instead of simply identifying exposures, it continuously validates risk, simulates potential attack paths, and automatically neutralizes vulnerabilities, which directly aligns with Gartner’s vision of autonomous interdiction.
Morphisec isn’t adapting to the future of cybersecurity. It’s already operating in it.
From Detection to Prevention: The New Security Standard
AI has changed the threat landscape. We believe, Gartner has validated the shift. And preemptive cybersecurity is quickly becoming the new standard. The question isn’t whether you need it. It’s whether your current security stack is capable of delivering it.
Download a complimentary copy of the Gartner Emerging Tech: Top Solution Capabilities in Preemptive Cybersecurity research to learn why detection-first security is no longer sufficient and how you can evaluate your current security posture.
1Gartner Emerging Tech: Top Solution Capabilities in Preemptive Cybersecurity, Luis Castillo, Isy Bangurah, David Senf, Elizabeth Kim, Charanpal Bhogal, Travis Lee, Carl Manion, published 1 April 2026
GARTNER is a registered trademark of Gartner, Inc. and/or its affiliates.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Morphisec.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.