From PLCs to Power Grids: The Cybersecurity Model is Breaking
Recent warnings from the Cybersecurity and Infrastructure Security Agency have made one thing clear: attacks on critical infrastructure are no longer hypothetical. They’re happening now, and they’re accelerating.
In its latest advisory, CISA detailed how Iranian-affiliated threat actors are actively targeting programmable logic controllers (PLCs)—the foundational systems that power water treatment facilities, energy grids, gas pipelines, and telecommunications networks.
But this isn’t just another threat alert.
It’s a signal that the cybersecurity model protecting critical infrastructure is fundamentally breaking down.
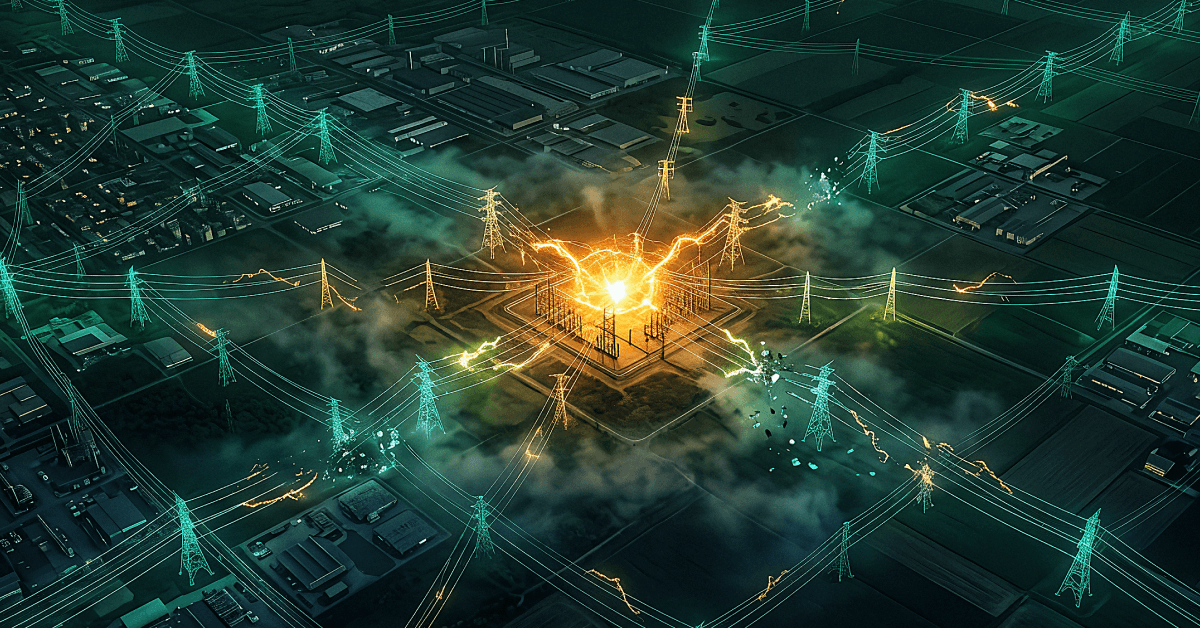
The Invisible Attack Surface Powering Modern Life
Critical infrastructure depends on a vast, interconnected web of operational technology (OT) and cyber-physical systems (CPS). At the center of it all are PLCs; devices designed to automate physical processes, not defend against modern cyber threats.
And there are a lot of them.
Across U.S. infrastructure sectors, estimates suggest there are between 600,000 and over 2 million PLCs in operation today. Water and wastewater systems alone account for more than 150,000 facilities, each with its own architecture, constraints, and security gaps.
These environments share a common reality:
- They rely heavily on legacy systems
- Many run outdated Windows and Linux operating systems
- They were never designed to be exposed to internet-connected threats
Over time, as IT and OT systems have converged, this infrastructure has become more efficient and exponentially more vulnerable.
The result is an attack surface that is not only massive, but increasingly difficult to defend.
AI Is Changing the Rules of Cyber Warfare
What makes this moment different isn’t just who is attacking…but how they’re attacking.
Threat actors are now leveraging AI to:
- Automate reconnaissance across vast OT environments
- Identify and exploit vulnerabilities at machine speed
- Adapt attack techniques in real time
This includes advanced tactics like fileless malware, living-off-the-land techniques, and polymorphic attacks that continuously evolve to evade detection.
In the context of PLCs and OT systems, attackers are:
- Manipulating SCADA displays to disrupt operations
- Exfiltrating sensitive project and configuration files
- Exploiting insecure ports and remote access pathways
- Establishing persistent access using lightweight tools like SSH backdoors
AI has fundamentally changed the tempo of attacks. And defenders are struggling to keep up.
Why Detection-Based Security Is Failing Critical Infrastructure
For years, cybersecurity strategies have been built around a simple premise: detect threats and respond quickly. That model no longer holds, especially in OT environments.
Here’s why:
- Detection Happens Too Late — By the time an attack is detected, it has often already executed, encrypting systems, disrupting processes, or exfiltrating data.
- Legacy Systems Can’t Be Secured Traditionally — Many OT systems cannot be patched or upgraded without operational risk. This creates persistent vulnerabilities that attackers can exploit indefinitely.
- Security Teams Are Overwhelmed — Critical infrastructure operators often lack the resources and visibility needed to monitor increasingly complex environments, especially against AI-driven threats operating at machine speed.
The result is a dangerous gap between attack velocity and defensive capability. And attackers are exploiting it.
A Necessary Shift: From Detection to Preemptive Cyber Defense
If detection is too slow, the answer isn’t better alerts. It’s eliminating the opportunity for attacks to succeed in the first place.
This is where preemptive cyber defense comes in.
Instead of waiting to identify malicious activity, preemptive approaches:
- Prevent exploits from executing
- Protect systems at runtime, where attacks actually occur
- Remove the predictability attackers rely on
This shift is especially critical in OT and CPS environments, where operational continuity is non-negotiable.
In an AI-driven threat landscape, organizations need environments that are resilient by design, not reactive by default.
What Preemptive Defense Looks Like in Practice
Modern preemptive security strategies are built around one core idea: make systems inherently
resistant to attack.
This includes approaches like:
- Automated Moving Target Defense (AMTD): Continuously randomizes system environments, preventing attackers from successfully exploiting known vulnerabilities
- Runtime Memory Protection: Stops fileless and memory-based attacks before they execute
- Adaptive Recovery Capabilities: Enables rapid restoration of systems and data in the event of disruption
Together, these capabilities shift security from a reactive posture to a proactive one, where attacks fail before they can cause harm.
The Stakes: More Than Data, It’s Operational Stability
When critical infrastructure is compromised, the impact goes far beyond IT systems. It affects:
- Access to clean water
- Reliability of energy and gas supply
- Stability of telecommunications networks
- Continuity of essential services
These are not isolated incidents; they are systemic risks with the potential for cascading consequences across industries and communities. In this context, cybersecurity is no longer just a technical issue.
It’s a matter of public safety and economic resilience.
What Leaders Should Do Now
For CISOs, operators, and infrastructure leaders, the path forward requires a fundamental shift in strategy.
Key priorities include:
- Eliminate Internet-Facing Exposure: Segment and isolate PLCs and OT systems from public networks
- Strengthen Access Controls: Implement secure gateways, MFA, and strict authentication for remote access
- Adopt Layered Security: Combine traditional controls with runtime and preemptive protection mechanisms
- Invest in Prevention-First Technologies: Shift focus from detection and response to stopping attacks before execution
Most importantly, organizations must rethink what “secure” means in an AI-driven world.
The Future of Critical Infrastructure Security
AI-powered threats are not slowing down. They are becoming faster, more adaptive, and more autonomous. At the same time, the systems they target (PLCs, SCADA, and OT environments) remain some of the most exposed and least protected assets in the modern enterprise.
The question is no longer whether these systems will be targeted. It’s whether organizations can prevent attacks before they begin.
How Morphisec Helps Secure Critical Infrastructure
Morphisec’s Adaptive AI Defense capabilities are purpose-built to address the realities of modern cyber threats, especially in environments where detection alone is not enough.
By combining Preemptive Cyber Defense, AMTD, runtime memory protection and adaptive recovery capabilities, Morphisec enables organizations to stop attacks before they execute, protect operational continuity, and build true cyber resilience across IT and OT environments.
Explore how Morphisec is helping organizations defend against AI-driven threats and book a demo to see Morphisec in action.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.