Gone in an Hour: Why Law Firms Can’t Afford to Ignore Data Exfiltration Risks

In today’s breach economy, speed is everything — and attackers are faster than ever.
Gone are the days when data exfiltration was a slow, stealthy process. According to Verizon’s 2025 Data Breach Investigations Report (DBIR), most attackers now exfiltrate sensitive data within hours of gaining access. And for law firms — where client confidentiality is sacrosanct and sensitive data is abundant — the stakes couldn’t be higher.
Whether it’s litigation strategy, M&A deal flow, or privileged communications, law firms are prime targets for threat actors. Worse still, many firms operate with lean IT teams and limited cybersecurity expertise, leaving them vulnerable to the fast-evolving tactics of modern cybercriminals.
Data Exfiltration: A Growing and Accelerating Threat
Data exfiltration refers to the unauthorized transfer of data from a network to an external destination. It’s the critical inflection point in a breach — the moment attackers’ cash in on their access.
And it’s happening faster than ever.
According to Verizon’s 2025 DBIR, once attackers gain initial access:
- The median time to exfiltrate data is less than one day.
- More than 50% of breaches that involve system intrusion also include confirmed data exfiltration.
- Stolen credentials and exploited vulnerabilities are often the enablers, with attackers moving quickly to identify, access, and siphon off high-value data.
For law firms, that window of exposure is perilously short — especially when many don’t have preemptive cyber defense capabilities to stop threats before they cause damage.
Double Extortion and Ransomware: Adding Insult to Injury
Data exfiltration isn’t just about quiet theft anymore — it’s a lever for extortion.
Modern ransomware attacks often use a double extortion model: First, the attacker exfiltrates your firm’s sensitive data. Then, they encrypt your systems and demand a ransom. If you don’t pay, they threaten to publish or sell stolen data on the dark web.
Verizon found that:
- Ransomware appeared in 44% of breaches in 2024, a 37% year-over-year increase.
- Many of these cases involved exfiltrated data, not just encryption.
- And despite stronger defenses at larger enterprises, small to mid-sized firms were hit hardest — 88% of ransomware-related breaches occurred in SMBs.
In other words: if you’re a smaller or mid-sized law firm, and you think you’re too small to be targeted — think again.
The Cost of Ignoring Exfiltration Prevention
A successful exfiltration attack on a law firm can have far-reaching consequences, including:
Client Trust Erosion — A breach of sensitive client data directly impacts your relationships and credibility. Losing client trust can result in significant business losses.
Regulatory Fines — Data breaches often lead to non-compliance penalties under regulations like GDPR or industry-specific laws, which can reach millions of dollars.
Reputational Damage — The public disclosure of a breach can tarnish your firm’s reputation and lead to client loss.
Operational Disruption — Even if encryption is avoided, exfiltration incidents require costly investigations, legal responses, and remediation efforts.
For law firms, prevention is not just a security strategy—it’s a business and ethical mandate.
How Morphisec Helps Law Firms Stop Exfiltration Before It Starts
Preventing exfiltration requires stopping attackers before they can establish footholds or move laterally through your environment. That’s where Morphisec’s Exfiltration Prevention — a core component of its Anti-Ransomware Assurance Suite — comes in.
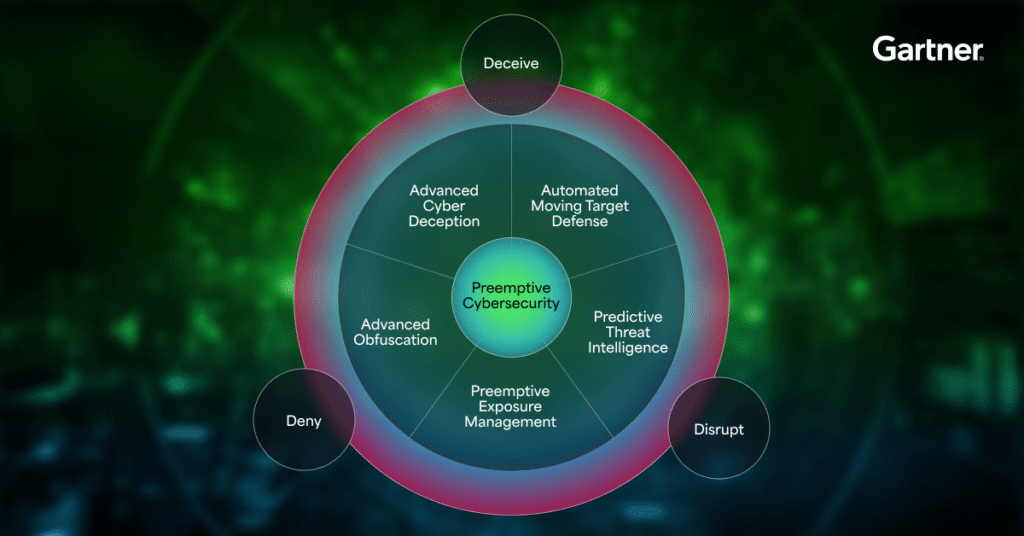
Morphisec uses a prevention-first approach that blocks data exfiltration attempts in real-time by:
- Preventing attackers from discovering or accessing sensitive data using deception and polymorphic moving target defense (AMTD) techniques.
- Blocking malicious exfiltration channels, including command-and-control traffic, clipboard grabs, and screen scraping, that attackers use to extract information.
- Protecting endpoint memory and processes, eliminating common exfiltration behaviors like credential theft or keystroke logging before they can succeed.
Because Morphisec operates silently and without signatures, it’s able to stop even the most advanced or unknown threats — including fileless malware and zero-day exploits — before data ever leaves your firm’s network.
| Exfiltration Technique | Addressed by Morphisec? | Description | Frequency |
|---|---|---|---|
| Exfiltration Over Web Services | Yes | Blocks unauthorized uploads to cloud services. | 17% |
| Transfer Data to Cloud Accounts | Yes | Prevents tools like Rclone and unauthorized cloud use. | 9% |
| Exfiltration Over C2 Channels | Partially | Disrupts most C2 channels, with some encrypted exceptions. | 8% |
| Automated Exfiltration | Yes | Stops automated scripts and tools in real time. | 9% |
And the best part? There’s no need to chase down alerts or perform forensics after the fact — Morphisec stops exfiltration activity in its tracks, with zero dwell time.
Prevention is the Best Defense
As a law firm, your reputation and your clients’ trust depend on your ability to protect their data. In a world where ransomware attackers have moved beyond encryption to exfiltration and double extortion, prevention-first security is critical.
Morphisec’s Exfiltration Prevention provides the confidence you need to operate securely, knowing that your client data—and your firm’s reputation—are protected. With Automated Moving Target Defense, seamless integration, and a 100% Ransomware-Free Guarantee, Morphisec is the ultimate solution for law firms ready to stay ahead of today’s most sophisticated threats.
Ready to safeguard your firm? Request a demo today and see how Morphisec can protect your law firm from data exfiltration and ransomware.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.