Ransomware Prevention
Stop Stealthy Ransomware Attacks
Detect and stop ransomware across the MITRE ATT&CK chain.
Stop ransomware attacks that traditional technologies miss
Protected companies
Protected endpoints
Attacks addressed daily
How Anti-Ransomware Assurance Works
Powered by Automated Moving Target Defense, Morphisec offers comprehensive preemptive cyber defense with three distinct security layers that prevent ransomware, without affecting productivity or performance.

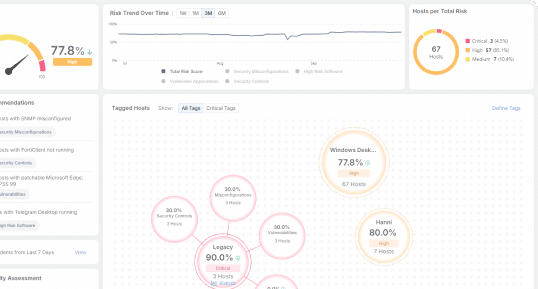
Adaptive Exposure Management
AEM elevates your security posture by prioritizing vulnerabilities, automating the assessment of your security controls, identifying high-risk software and addressing security misconfigurations.
Infiltration Protection
Infiltration Protection enhances your organization’s cyber resiliency by continually changing the attack surface, rendering the target unpredictable and harder for attackers to exploit.
Impact Protection
Impact Protection that proactively defends critical assets and data, minimizing recovery times and strengthening your anti-ransomware stance for true ransomware protection.
Adaptive Recovery
Adaptive Recovery both ensures encrypted files are restored quickly and preserves critical forensic data in tamper-proof storage, enabling fast incident investigation and comprehensive recovery.
Ransomware prevention you can trust

Safeguard financial assets
Stop attacks at the earliest stage, preventing device encryption, business disruption, ransom payment demands, and loss of data and intellectual property.
Mitigate security gap risk
Morphisec offers a safety net and last line of defense that complements the technology you use today while enhancing it to catch the evasive and sophisticated attacks that they miss.
Ensure blast radius resiliency
Adapt, protect and defend with a multi-layered guard that proactively prevents attacks at multiple phases and protects critical system resources and data when ransomware attempts to execute, reducing mean time to recovery.
Benefits of a prevention-first strategy
Boost your security posture
- Gain improved visibility into threat exposure for better preparation
- Enable Rapid Response and recovery to minimize downtime
- Ensure operational readiness to effectively handle potential threats
Maximize value and TCO
- Save on deployment, maintenance, support, training, and decommissioning costs
- Reduce time and costs for tech resources with Morphisec’s threat prevention
- Enhance the performance of existing detection and response tools with Morphisec
Gain assurance
- Ensure continuous defense, protecting your organization even if other safeguards fail
- Mitigate risks with better visibility into shadow IT, misconfigurations, and high-risk software
- Boost efficiency by reducing attack dwell time and recovery
“The tool has been proven to stop ransomware attacks over and over again, both in lab environments, and in the wild. Zero-day exploits are also protected against.”
“Morphisec specifically protects against ransomware and zero-day attacks, needs only a small footprint to run… and allows us the flexibility to continue using our current XDR and NextGenAV platforms.”
“Morphisec stops attacks in memory dead. We actually had an attempted ransomware attack and it wasn’t successful. Morphisec stopped that attack cold.”
Try Morphisec for Yourself
Take a free, self-guided tour of the platform and experience all that Morphisec has to offer.
Anti-ransomware assurance resources
Adapt, protect, and defend with the Anti-Ransomware Assurance Suite
Get a clear understanding of your attack surface, identify the unique factors that affect it, and gain the ability to address those factors before a ransomware attack.















