AI-Enabled Threats Demand Adaptive Cyber Resiliency
AI is no longer just a productivity tool. It’s a weapon.
Threat actors are using AI to automate reconnaissance, generate polymorphic malware, accelerate exploit development, and bypass traditional detection controls. The result? Faster breaches. Smarter evasion. Less dwell time before impact.
Meanwhile, most organizations are still defending with static, detection-heavy security stacks designed for a slower era.
If attackers are adaptive, automated, and AI-enabled, your security architecture must be too. That’s where Adaptive Cyber Resiliency comes in.
The Detection Problem in an AI-Driven Threat Landscape
For more than a decade, cybersecurity strategy has centered around detection and response.
Organizations have invested heavily in EDR, XDR, SIEM platforms, behavioral analytics, and threat intelligence feeds; all designed to identify malicious activity once it begins. The assumption has been simple: if we can detect it quickly enough, we can contain it.
AI-enabled threats are dismantling that assumption.
Modern attacks no longer rely on easily identifiable files or known signatures. Instead, they execute directly in memory, leverage legitimate system processes, and mimic normal behavior to blend into the environment.
Fileless techniques, process hollowing, shellcode injections, and credential abuse allow attackers to operate in ways that traditional monitoring tools struggle to distinguish from routine system activity. Even worse, many advanced threats actively tamper with security controls themselves, bypassing interfaces like AMSI or disabling hook-based inspection mechanisms before executing malicious code.
Detection tools, by design, depend on observable patterns. They rely on indicators of attack, behavioral baselines, or cloud-fed intelligence updates. But AI allows adversaries to continuously mutate their payloads, test against defensive stacks, and adapt their techniques in near real time.
The result is a shrinking window between initial access and operational impact. By the time alerts surface and analysts begin triage, the attacker may already have established persistence, escalated privileges, or initiated encryption.
In an AI-driven threat landscape, time-to-detection is no longer a reliable metric of success.
The speed and adaptability of modern attacks demand a different approach. One that does not depend solely on identifying malicious behavior after execution has begun but instead reduces the attacker’s ability to succeed in the first place.
Cyber Resiliency: A Strategic Shift from Reaction to Adaptation
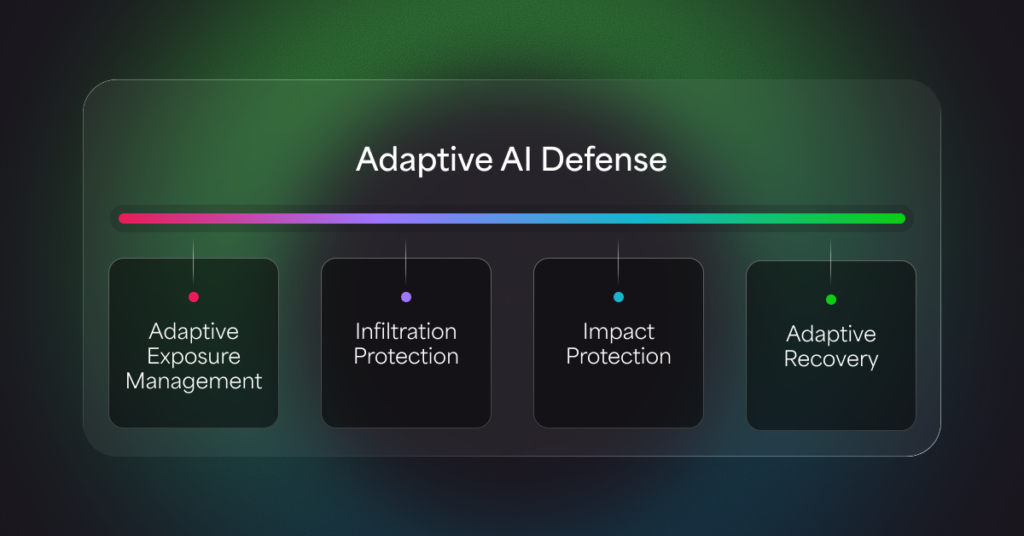
Adaptive Cyber Resiliency moves beyond reactive security. It is a strategy designed to:
- Anticipate emerging threats
- Withstand attack attempts
- Contain impact when compromise occurs
- Recover rapidly without business disruption
As detailed in the Achieving Adaptive Cyber Resiliency with Automated Moving Target Defense white paper, modern security architectures must evolve continuously, not just collect more telemetry.
Resiliency is no longer just about blocking malware. It’s about minimizing blast radius, protecting operational continuity, and ensuring business survival under active attack.
Continuous Threat Exposure Management: Necessary, But Not Sufficient
Security leaders increasingly adopt Continuous Threat Exposure Management (CTEM) to:
- Identify vulnerable assets
- Prioritize remediation
- Validate security controls
- Align security to business risk
This is critical.
But exposure visibility alone does not stop runtime exploitation.
AI-enabled threats don’t wait for patch cycles. They exploit vulnerabilities within days (sometimes hours) of disclosure. They bypass controls that rely on known signatures or historical behavior patterns.
Exposure management helps you understand risk.
You still need a way to neutralize it in real time.
Detection vs Deception vs Adaptive Defense
Here’s the architectural shift security leaders must consider:
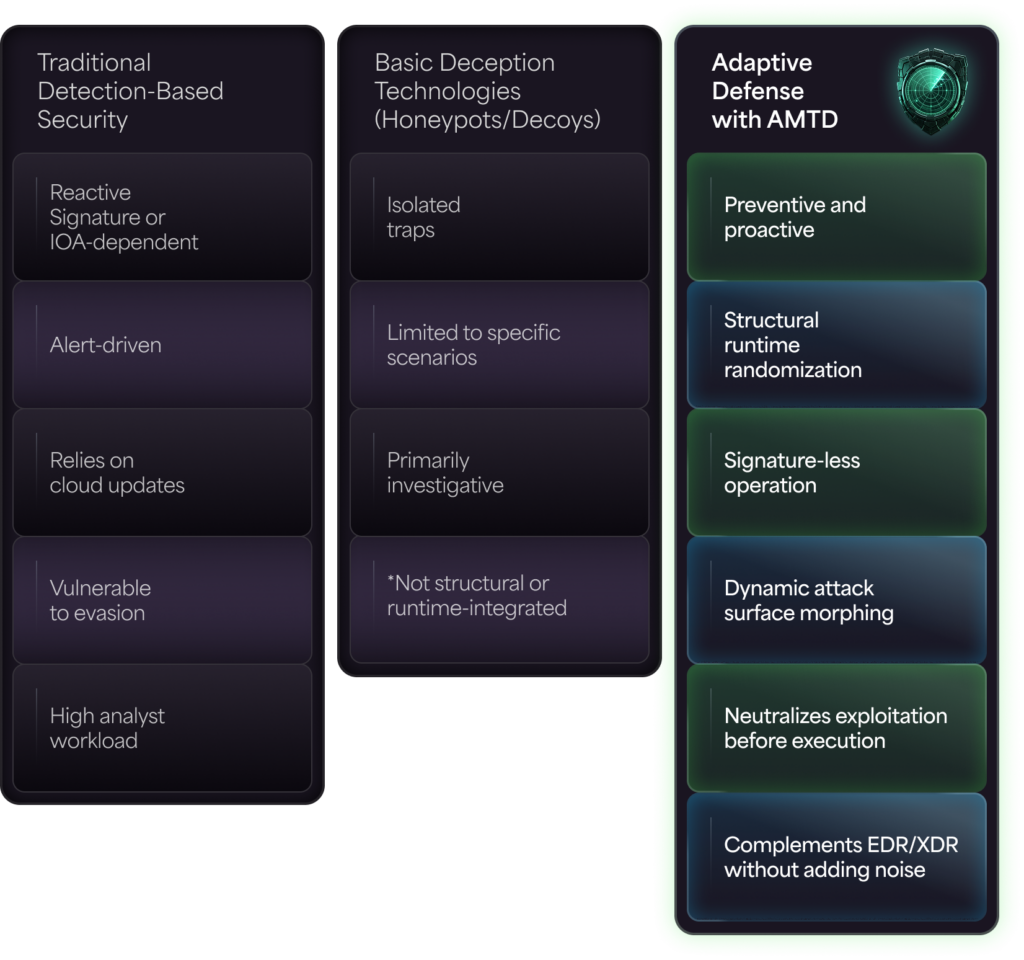
Detection tries to identify attacker behavior. Adaptive defense breaks attacker assumptions.
That distinction is everything in the AI era.
Automated Moving Target Defense (AMTD): Structural Deception at Runtime
AMTD introduces controlled dynamism into static computing environments.
Instead of inspecting behavior and hoping to catch malicious patterns, AMTD:
- Dynamically modifies memory allocation during process load
- Randomizes runtime structures
- Deploys traps in place of predictable memory locations
- Protects credential vaults and sensitive data stores
- Prevents shellcode injection, process hollowing, AMSI bypass, and in-memory ransomware
Unlike traditional hook-based systems that attackers can evade or disable, AMTD:
- Does not rely on signatures or IOAs
- Does not require constant cloud connectivity
- Does not depend on prior knowledge of attack techniques
It introduces structural uncertainty into the environment, forcing attackers to start reconnaissance from scratch every time.
In a world where AI automates attacker reconnaissance, unpredictability becomes a powerful defensive weapon.
Impact Protection: Minimizing Blast Radius
Resiliency is not just about prevention. It’s about reducing damage when something slips through.
AMTD-powered Impact Protection:
- Deploys decoy files that kill ransomware encryption processes at an early stage
- Prevents tampering with endpoint security controls
- Protects system recovery mechanisms
- Blocks credential theft and post-exploitation tools
- Reduces mean time to recovery
This layered approach ensures that even if an adversary attempts encryption or lateral movement, their ability to cause operational disruption is dramatically reduced.
The result is not just threat prevention. It’s business continuity protection.
Adaptive Exposure Management + AMTD + Adaptive Recovery
True Adaptive Cyber Resiliency combines three interconnected capabilities:
- Reduce Exposure — Adaptive Exposure Management identifies high-risk software, validates security controls, and prioritizes vulnerabilities in business context.
- Prevent Exploitation — AMTD neutralizes in-memory and fileless attacks before they execute; even zero-day threats.
- Minimize Impact — Impact Protection and adaptive recovery ensure rapid restoration of critical systems without extended downtime.
Together, these layers create a closed-loop defense model that evolves as threats evolve.
Why This Matters Now
AI-enabled threats will not slow down.
They will:
- Grow more autonomous
- Grow more evasive
- Target recovery systems
- Exploit detection blind spots
- Scale faster than security teams can respond
Security teams cannot hire their way out of this problem. They cannot alert-triage their way out of it either.
They need structural, automated, adaptive protection. They need defense that morphs faster than AI-powered attacks can adapt.
Build Security That Adapts Faster Than Attackers
The future of cybersecurity is not more alerts. It’s resilience. It’s deception. It’s adaptive architecture that neutralizes threats before they execute and minimizes damage when they try.
To learn how AMTD powers a truly adaptive security strategy, download Morphisec’s white paper.
Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.